Secure workforce access that Gets Out Of The Way.
Workforce Authority secures every user, device, and application from login to logout, modern and legacy, without replacing what you already have.
AI/ML Risk Assessment · Transaction Access · Adaptive Auth Security
80%
Reduction in credential-based attacks
Zero
Passwords to manage
< 1s
Risk score evaluation time
Problems We Solve
Authentication stops at the door. Everything After Login Is Trusted By Default.
Once a user passes MFA, their session is trusted indefinitely. Attackers know this and exploit it.
Passwords are a productivity tax.
Resets, lockouts, helpdesk calls, and recovery flows consume IT budget and employee time at scale. At enterprise scale, routine authentication issues create a steady cost in hours lost trying to log in and support tickets opened.
One login shouldn't mean twenty prompts.
Modern SaaS apps get SSO. But legacy apps, VPNs, and on-premises systems still demand separate credentials, repeated logins, and browser re-authentication mid-session. The result is a fractured workday, a fragmented user experience, and a growing credential burden for IT.
The device is verified. The person isn't.
Standard endpoint authentication trusts the machine, not the human behind it. Without a three-way bind among the user, the device, and a trusted mobile authenticator, shared workstations and rotating endpoints create sessions that belong to hardware rather than to an identity your organization controls.
MFA friction that employees resist
Push fatigue, SIM-swap risk, and prompt-heavy flows don't just frustrate users; they generate pressure to reduce authentication requirements entirely. When security control becomes a usability problem, the organization eventually trades one for the other.
Internal Workforce Access
Core Capabilities
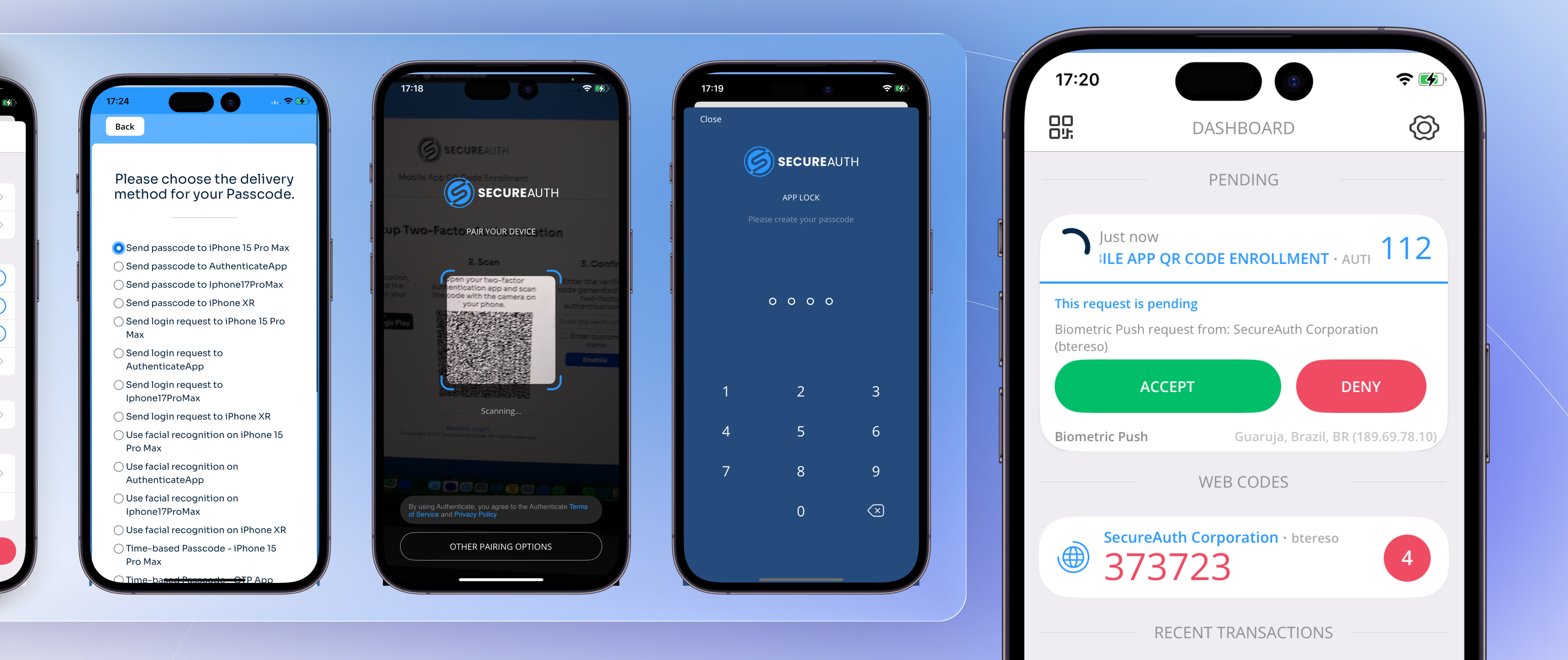
Make phishing structurally impossible.
- The SecureAuth mobile app generates a device-bound private key in hardware that never leaves the device, requiring cryptographic proof rather than human approval.
- Push bombing, MFA fatigue attacks, and SIM-swapping have no attack surface against a key that cannot be extracted or intercepted.
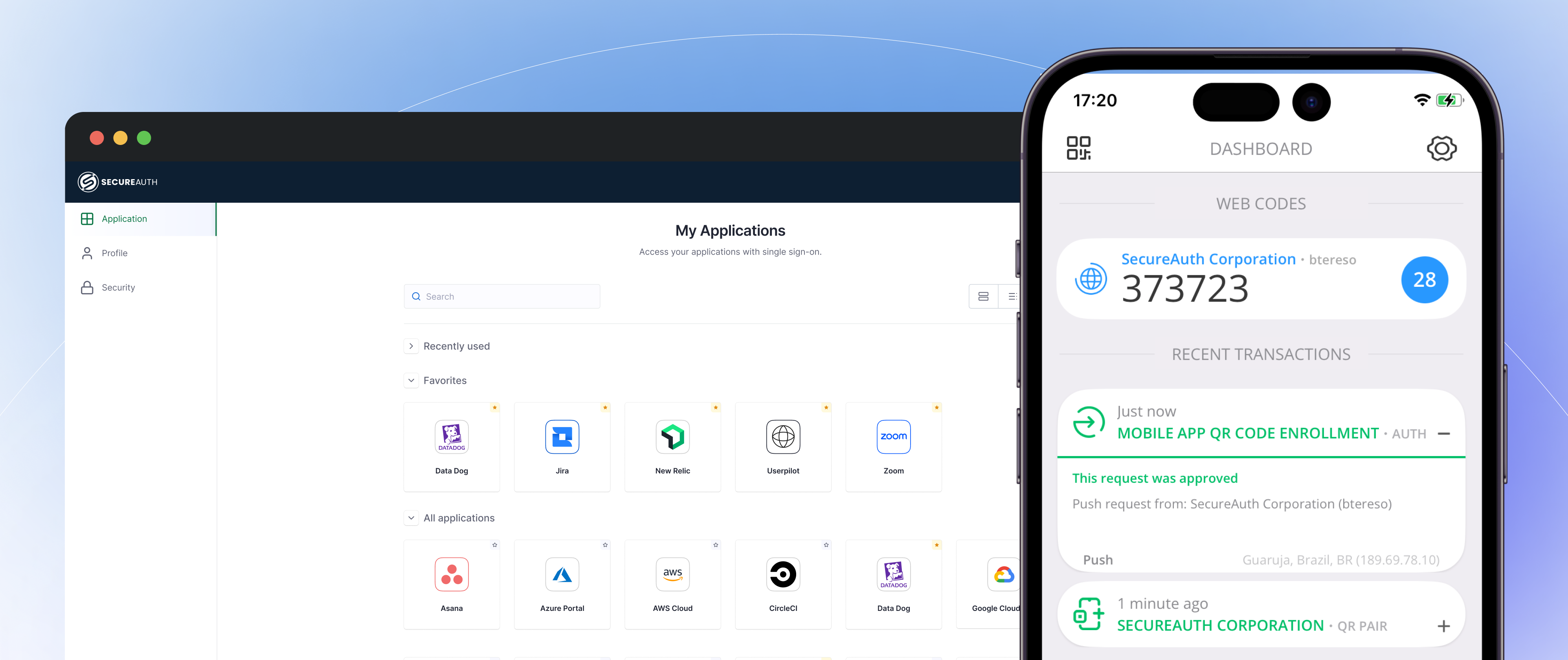
One login. Every app. All day.
- The endpoint agent-to-web SSO bridge extends a trusted session across cloud and on-prem applications.
- Users move between apps without repeated MFA prompts while maintaining consistent security across every connected service.
Enforce identity before the OS grants access.
- Endpoint Trust binds the user and device at the workstation session level before the operating system, and application access is granted.
- Shared endpoints, rotating workstations, and offline environments are supported without relying on cloud connectivity.
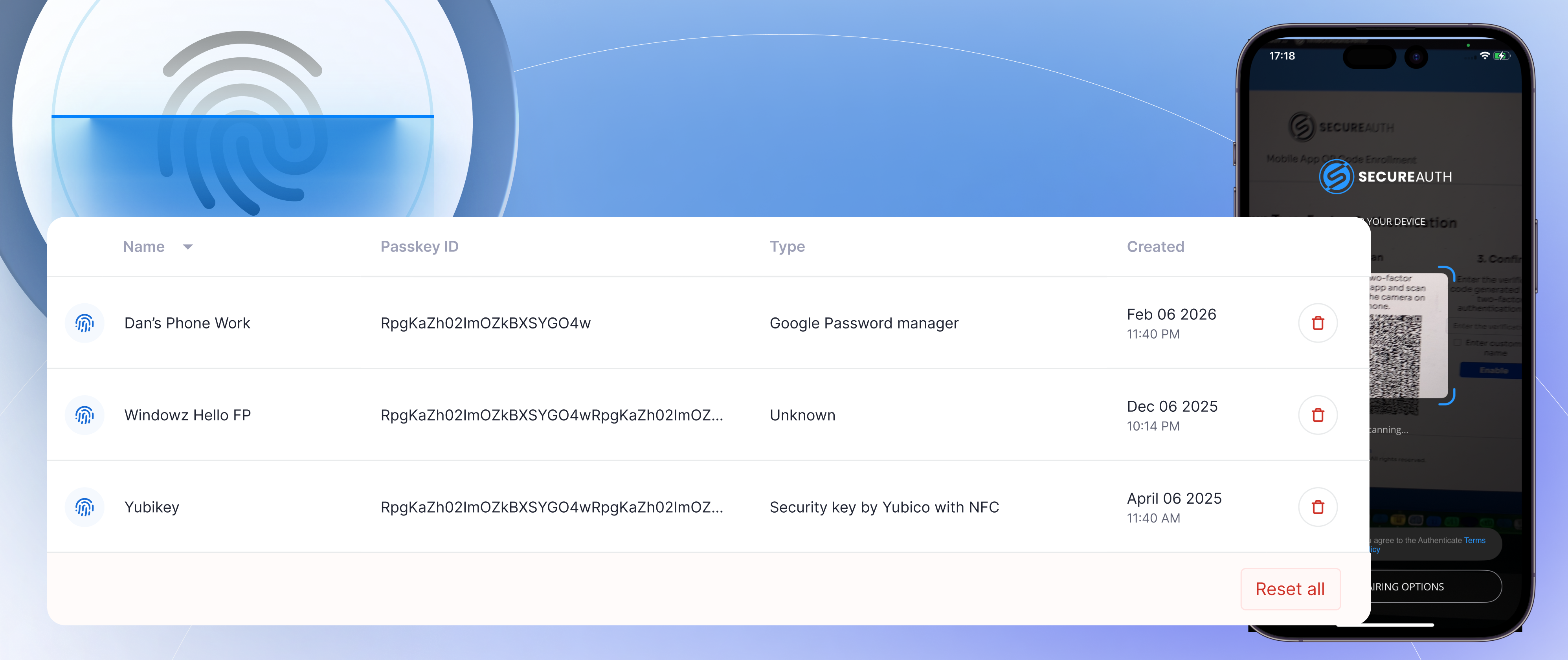
Organization-Controlled Credentials
- The SecureAuth Enterprise passkeys are issued and controlled by your organization, not by Apple, Google, or any consumer platform.
- Passkeys operate beyond the browser, support offline environments and recovery scenarios, and persist through staff lifecycle changes without credential re-issuance.
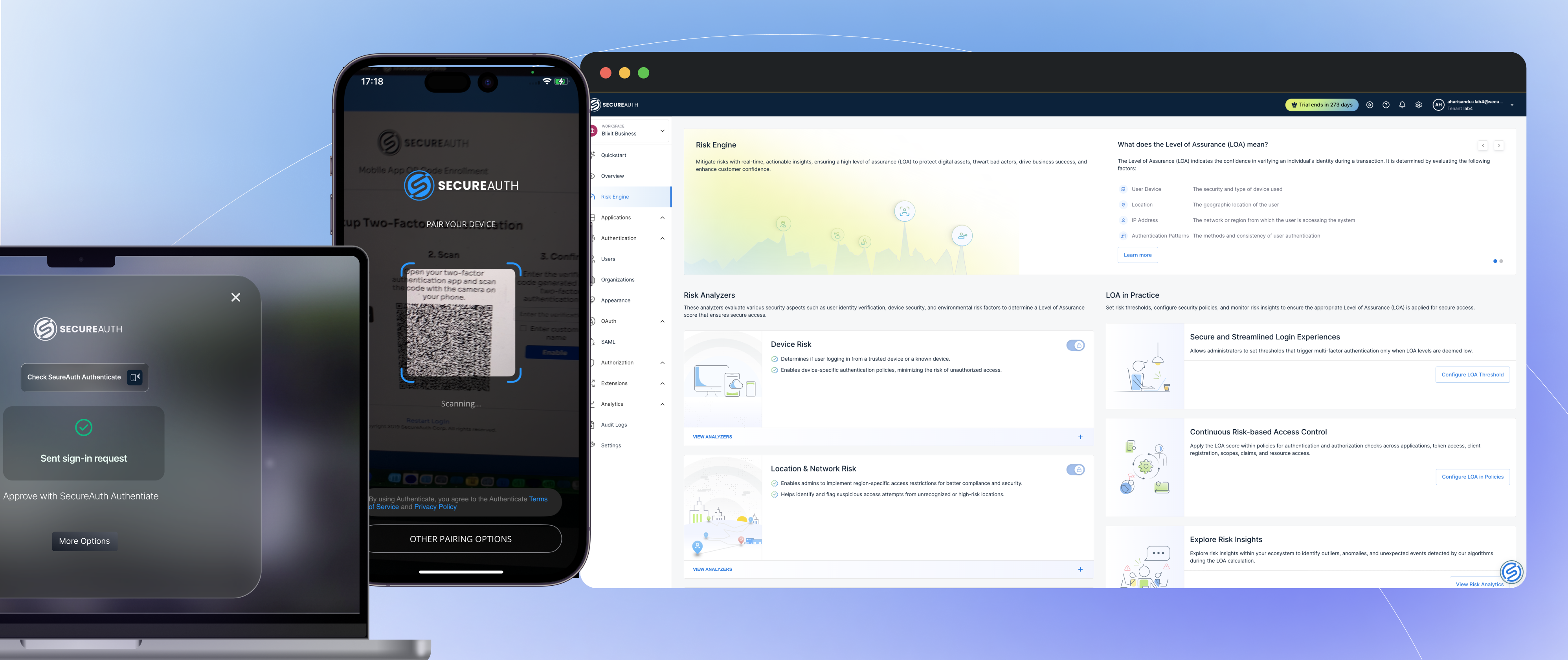
More security. Fewer prompts.
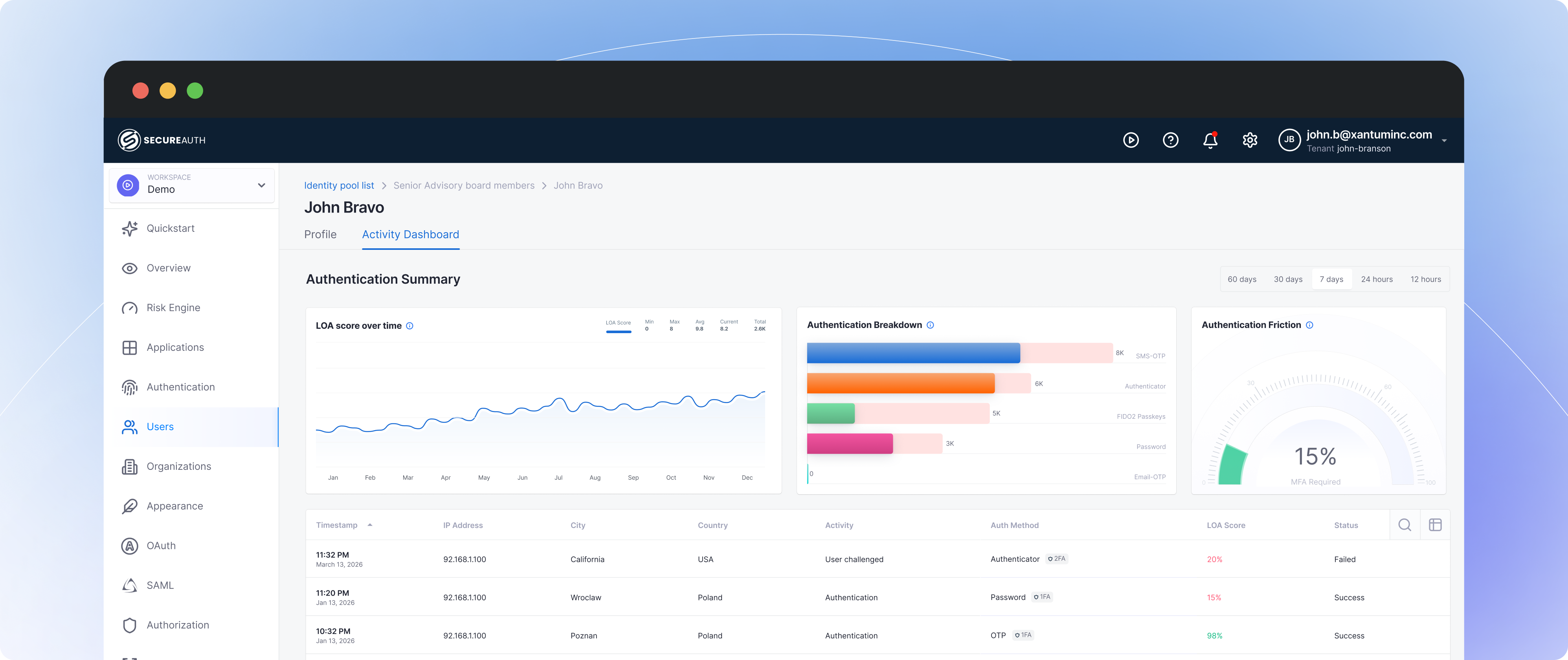
- High-risk sessions are challenged when risk changes. Access policy adapts in real time based on device trust, location, and behavior.
- Low-risk sessions move through with less friction. Users notice when signals indicate elevated risk.
Your Employees' Sessions Are Your Largest Unmonitored Attack Surface.
80% of breaches involve compromised credentials. Static MFA doesn't protect what happens after login.
Post-login session monitoring
Continuous risk scoring throughout the session. Anomalous behavior triggers step-up auth or termination, not just a stale login check.
Zero standing privileges
Just-in-time access grants that expire automatically. No more accumulated permissions from role changes over the years.
Phishing-resistant by design
FIDO2 passwordless auth eliminates the credential vector entirely. No password means nothing to phish.
80%
Of breaches involve compromised credentials (Verizon DBIR)
7 hrs
Average session hijack detection time
70+ passwords
Average employee credential burden
Ready to see how Workforce Authority secures Your Workforce?
Schedule a technical walkthrough, no deck, just your actual use case.
Request a Demo