B2B Identity Management That Scales With Your Partners
B2B Authority is built to support enterprise access control at scale. Where business customers and partners already have their own admins, org structures, and access policies. Your identity platform should support them all.
Delegation Without Sprawl · Deploy Anywhere · Multi-IdP
90%
Faster partner onboarding
200+
Partner orgs in one tenant
60%
Lower TCO vs. legacy IAM vendors
Problems We Solve
Identity Risk Increases As Businesses Scale
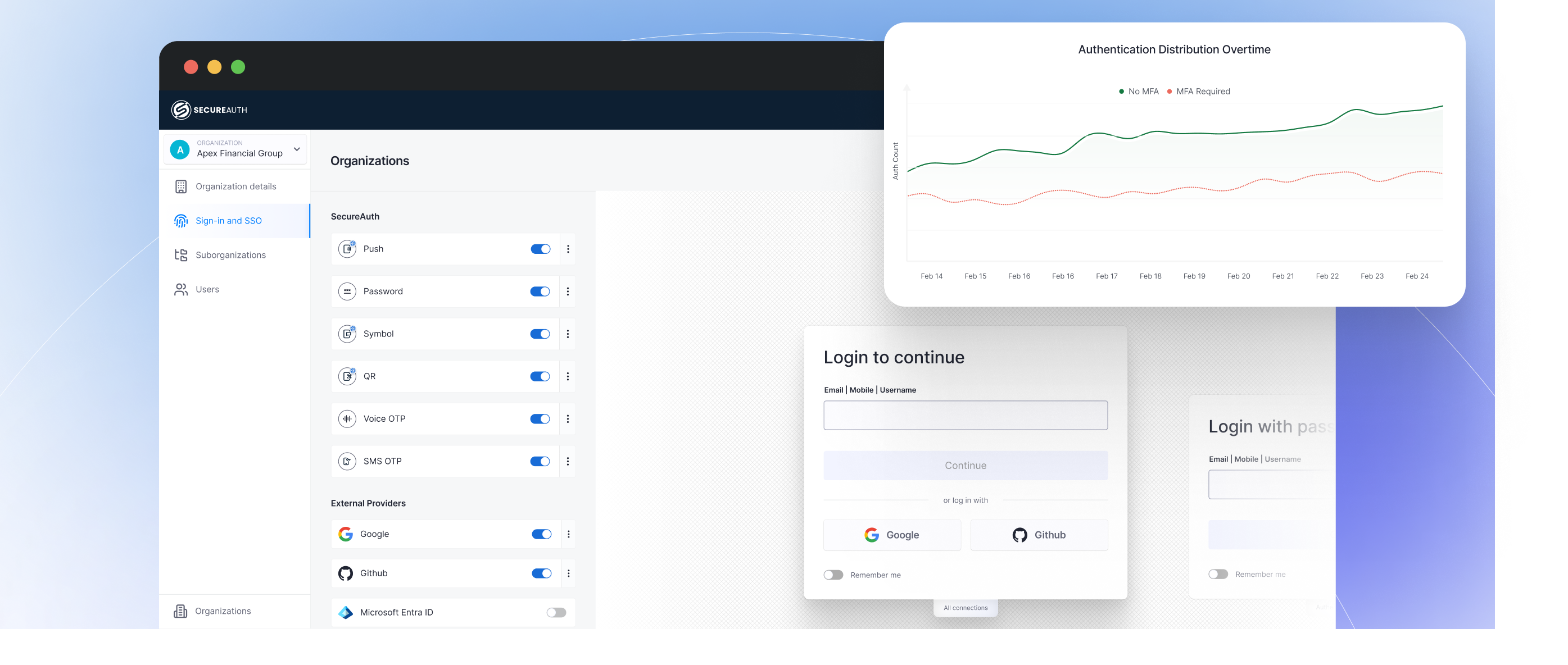
Enterprise Clients Don't Flex on SSO
Enterprise SSO has always been a standard expectation. But when every enterprise client requires user provisioning, deprovisioning, and authentication using OIDC, OAuth, SAML, and SCIM or custom mechanisms, engineering gets pulled into every deal and competitors close faster.
Access Sprawl at Scale
Controlling who has access to what is foundational to securing a B2B ecosystem. But traditional IAM was never built to accommodate business customers, partners, and clients at scale. Stale entitlements, role explosion, and shadow admin roles accumulate silently until a security incident exposes the gap.
Flat Models Break Org Hierarchies
Modeling how businesses actually operate has always been a baseline expectation. But when your identity layer only supports flat user models, every holding company, sub-merchant, and reseller becomes a manual workaround your engineering team didn't budget time for.
Shared Partner Policies. Shared Risk.
Legacy identity systems offer no true isolation between sub organizations. When a single configuration change cascades across every client environment, compliance stops being a guarantee and becomes a gamble no enterprise buyer will accept.
BUILT FOR THE COMPLEXITY OF B2B
Core Capabilities
Multi-Org Hierarchies Without Custom Code
- Model business customers, holding companies, resellers, sub-merchants, and branches natively with unlimited nesting depth and no custom code required.
- Enforce top-level access control across every entity, giving security teams centralized visibility from a single control plane.
- Scale organizational structures without rework, as each new tier automatically inherits the policies set above it.
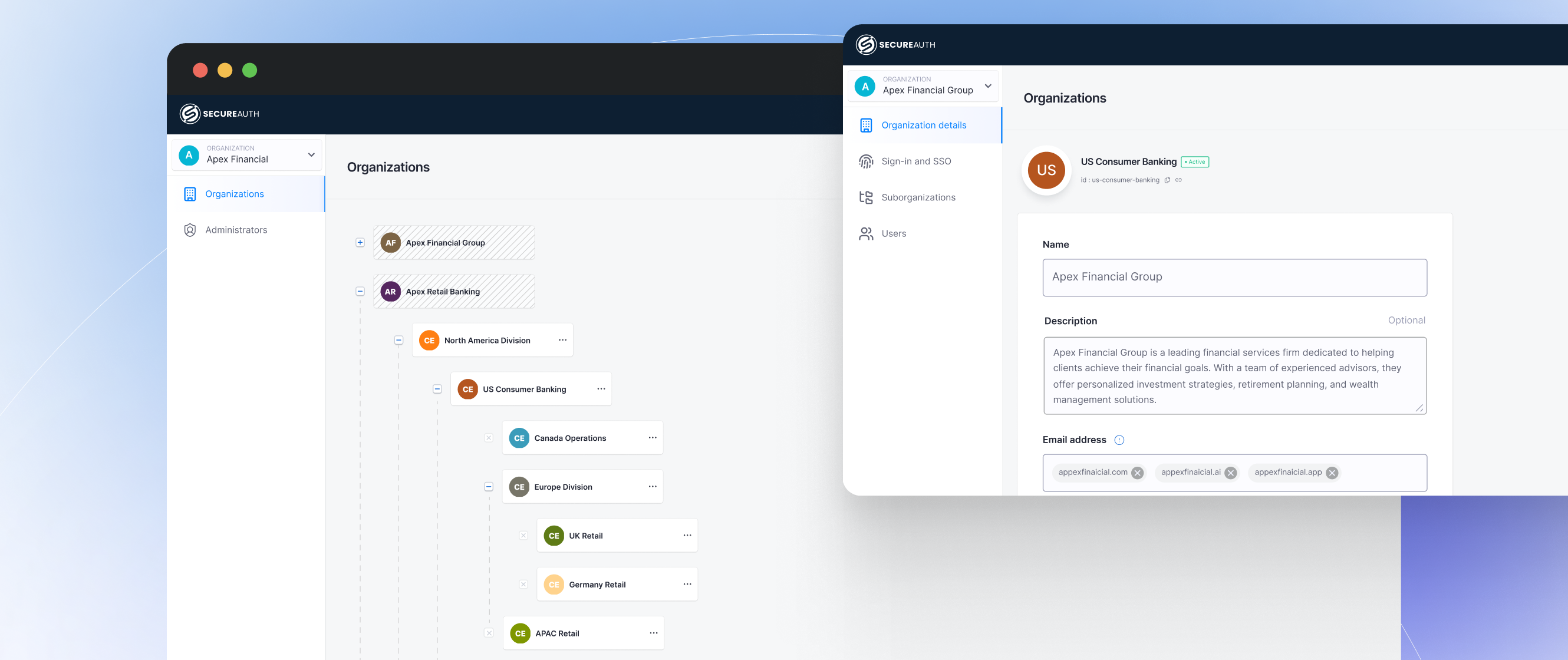
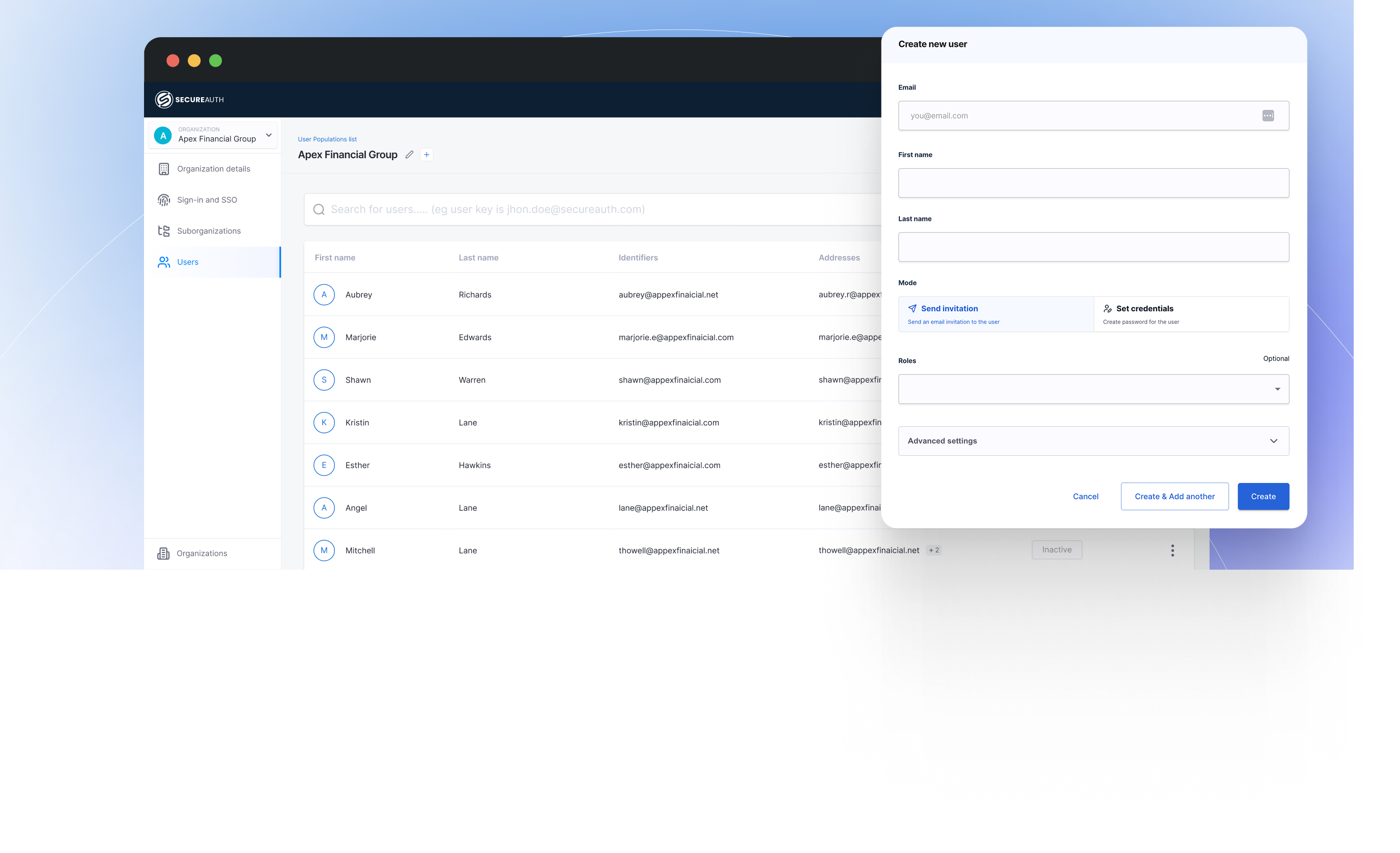
Delegate Control With Self-Serve Administration
- Remove the provisioning bottleneck by letting enterprise clients manage their own users, roles, and security policies through a branded self-service portal.
- Enforce platform-wide guardrails that define the boundaries so partners operate freely within them, never outside them.
- Eliminate routine access requests from your support queue without giving up oversight of who can do what.
Connect Any IdP. Onboard Faster.
- Federate any enterprise identity provider over SAML, OIDC, or SCIM with intelligent IdP discovery and zero custom protocol work.
- Enable self-service onboarding so enterprise clients connect their existing IdP without engineering involvement on either side.
- Stop losing deals to onboarding delays and turn identity integration from a blocker into a competitive advantage.
Authorization at Action-Level Enforcement
- Stop assuming access is safe because it was granted at login and evaluate every API call against role, org tier, and transaction type at the point of execution.
- Enforce least-privilege access with scoped OAuth tokens and fine-grained policy-driven authorization across every microservice and integration.
- Gate high-value transactions with approval flows that require explicit authorization, not assumed permission.
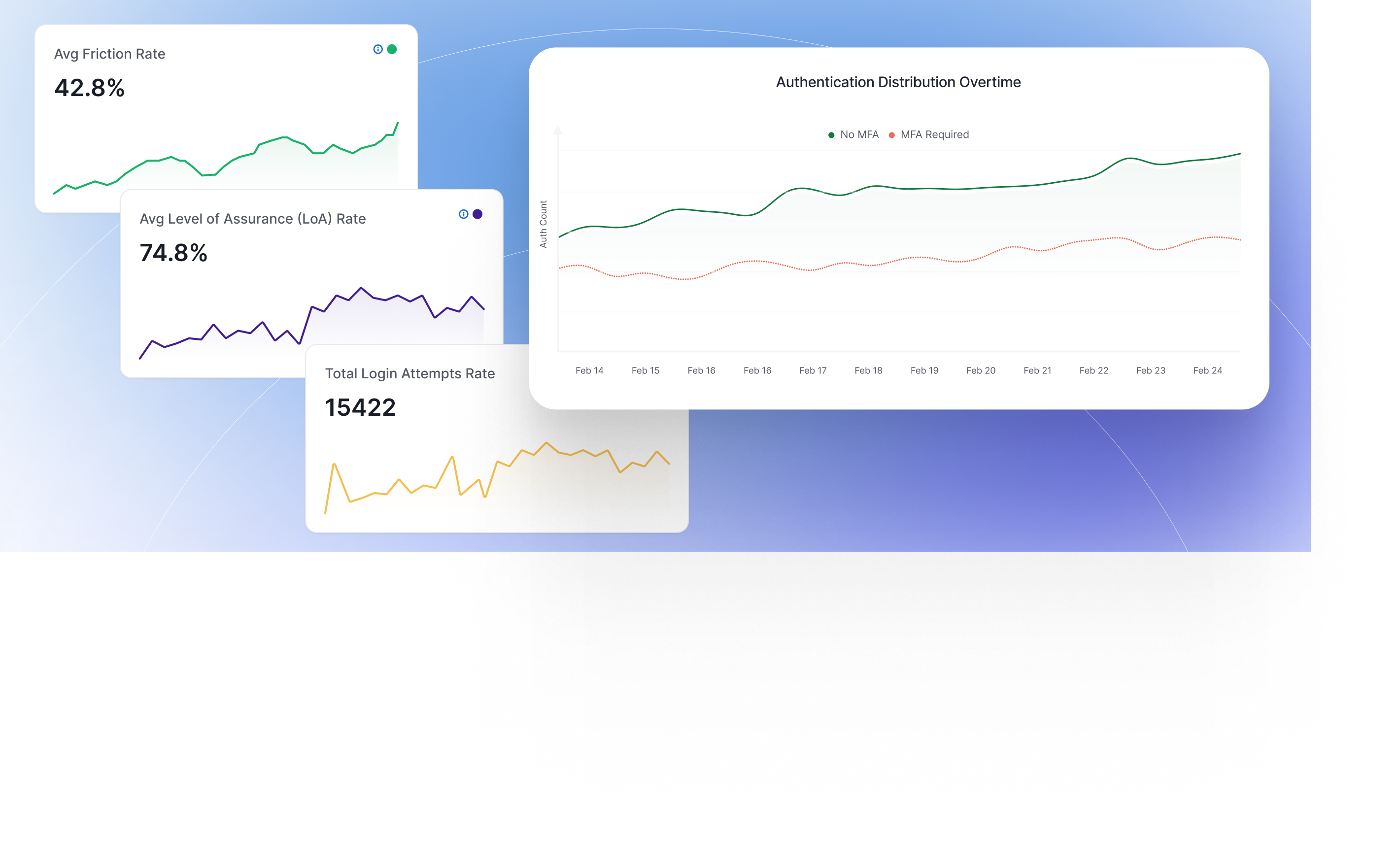
Your Business Customers' Access Is Your Attack Surface. Do You Have Visibility?
62% of breaches involve third-party access. Most teams find out too late because customer and partner sessions are a black box.
Complete audit trail, automatically
Every customer org login, privilege change, and API call is logged. SOC 2, PCI-DSS, HIPAA evidence is already there, no manual compilation before your next audit.
Revoke access instantly
When a customer org's credentials are compromised, you don't have 3 days to track down every access point. B2B Authority terminates sessions across your platform in seconds.
Risk scoring that stays active
Continuous session scoring means you're not relying on a check from 6 hours ago. Anomalous behavior triggers step-up auth or termination, in real time.
$4.45M
Average cost of a data breach (IBM 2023)
62%
Of breaches involve third-party access (Verizon DBIR)
4-6 weeks
Average time spent on manual audit prep before B2B Authority
Ready to see how B2B Authority handles Your Ecosystem?
Schedule a technical walkthrough, no deck, just your actual use case.
Request a Demo