Continuous Risk Mitigation, Every Session
Assurance Authority assesses identity access risk in real-time, to monitor and detect suspicious behavior prior to login and during the session. Device trust, behavioral signals, geolocation, and IP reputation are evaluated in parallel, so risk is measured at every moment.
Continuous Trust · Real-Time Risk Scoring · Adaptive Policies
< 1min
Threat detection vs. 204 day average
4
Signal categories aggregated
Real-time
Continuous trust evaluation
Problems We Solve
Identity Threats Live Between Authentication Events
Risk That Doesn't Stop at Login
Most platforms evaluate risk once, at the point of authentication, then go silent. Threats that emerge from mid-session, including lateral movement, anomalous behavior, and account abuse, go undetected because no one is watching after the gate opens.
Valid Logins Aren't Enough
Valid credentials no longer mean a legitimate user. Attackers log in with stolen passwords, replayed tokens, and hijacked sessions, and standard authentication has no way to tell the difference. Once access is granted, the threat is already inside.
Attackers Don't Announce Their Location
A legitimate user does not authenticate from London and Singapore within the same hour. Without geolocation analysis and IP reputation at login, impossible travel and risky origins blend in with legitimate traffic.
New Devices Signal New Risk
A familiar password from an unrecognized device is one of the clearest early indicators of account compromise. Without device trust scoring tied to authentication history, there is no mechanism to distinguish a user's known endpoint from an attacker.
CONTINUOUS RISK INTELLIGENCE FROM PRE-LOGIN TO SESSION END
Core Capabilities
Risk Scoring To Stop Mid Session Threats
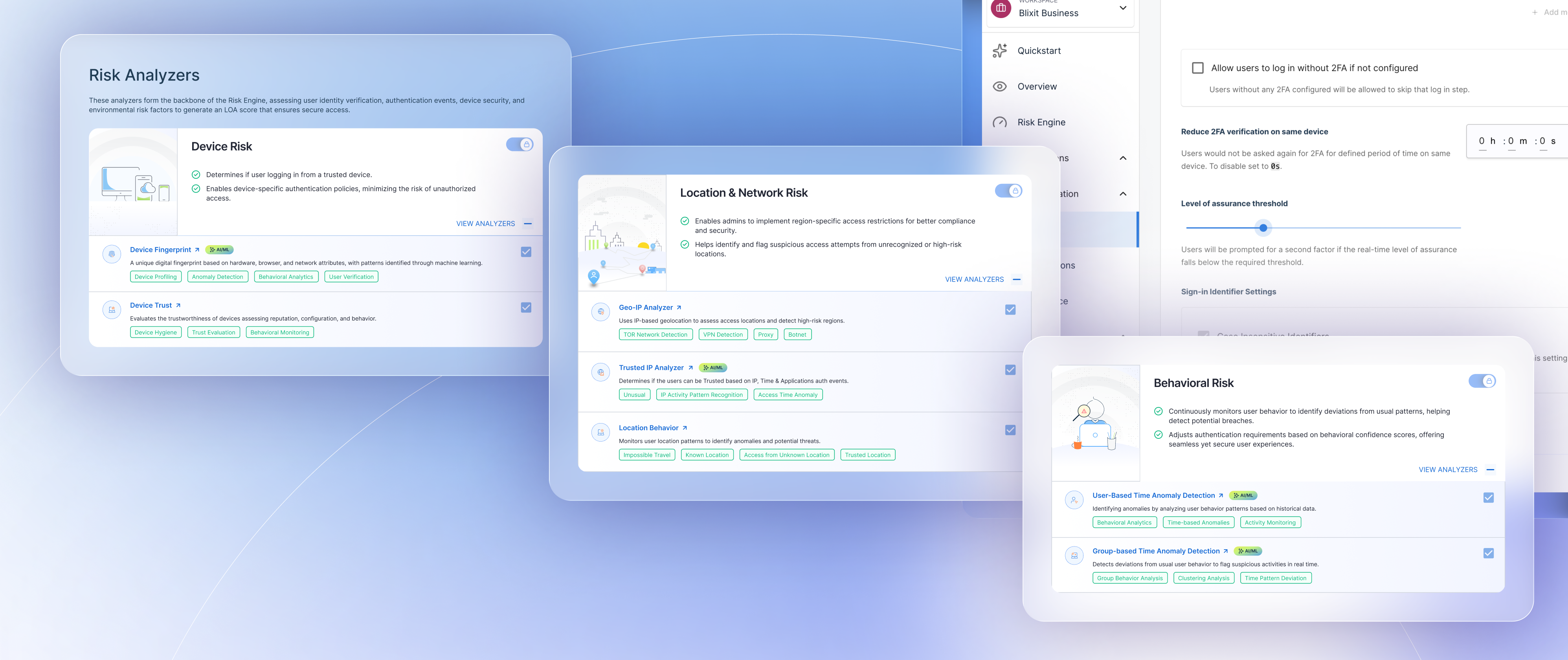
- Score risk in real time as device, behavioral, and location signals change to continuously assess the level of assurance throughout the session.
- Assess behavioral patterns across the full session using user-specific ML models trained on location, device, application, and time-of-use history.
- Identify geographically implausible login sequences and IP location inconsistencies that indicate credential reuse or session impersonation across boundaries.
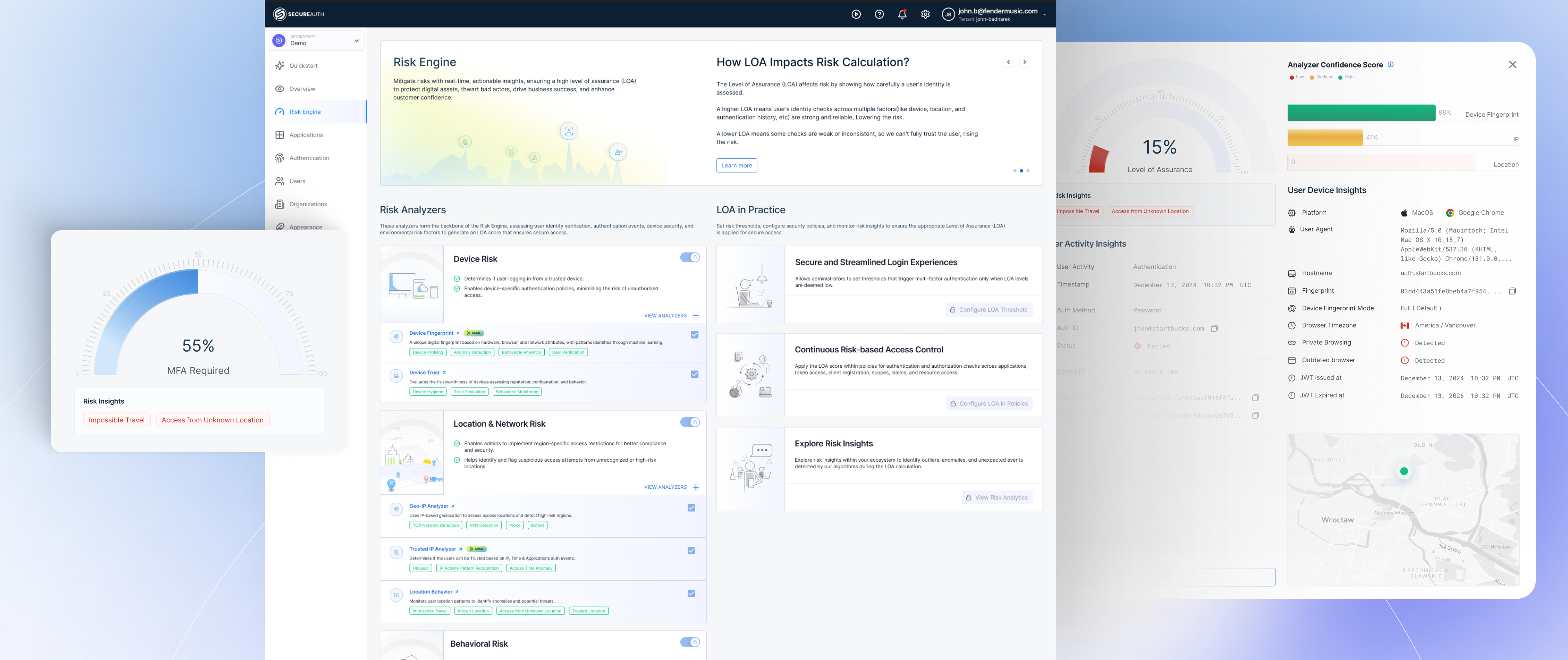
Authentication Friction That Follows Risk
- Increase or decrease authentication friction dynamically based on the LOA score for each individual session, not keyword-matched conditions applied uniformly across all users.
- Establish trust combinations of device, location, and access time per individual, so legitimate behavioral variation does not generate unnecessary step-up challenges.
- Define organizational conditions, trusted network ranges, known devices, and group membership rules under which MFA friction is reduced without changing the underlying risk posture.
Real-Time Risk Scoring Across Every Signal
- Analyze every signal simultaneously, from device fingerprint and IP reputation to geolocation, behavior, and third-party threat intelligence, so each signal is evaluated in the context of every other.
- Combine risk weights into a single LOA score with adjustable domain and analyzer weights, so risk decisions reflect organizational priority, not fixed defaults.
- Correlate across domains and identify threat patterns that individual signals obscure by evaluating device, network, and behavioral inputs as a unified set rather than independent data streams.

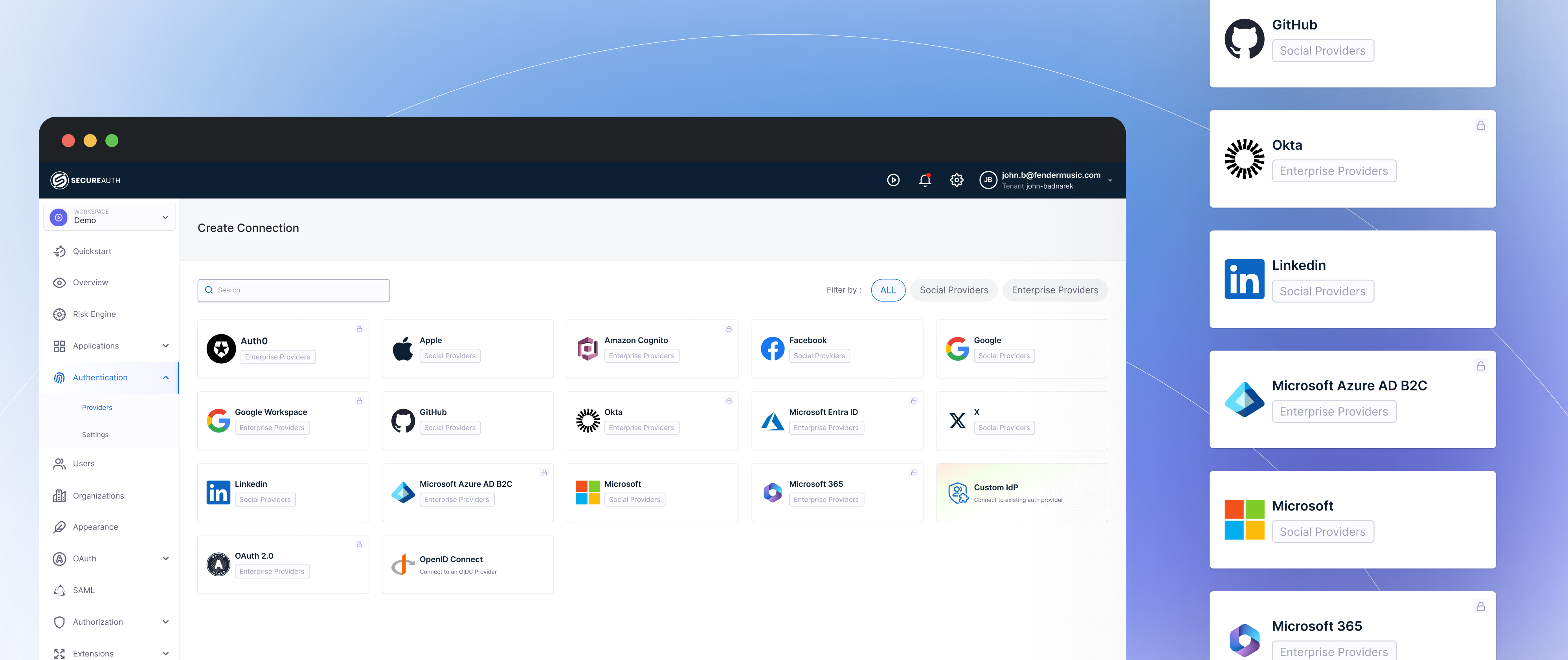
Drop Into Any Identity Provider Without Disruption
- Connect to Okta, Ping or any identity provider through a modular overlay that operates independently without modifying existing directory integrations or policy configurations.
- Start scoring immediately without disrupting authentication flows, team workflows, or the deployment cycle of the underlying identity platform.
- Configure, enable, disable, or reweight analyzers per tenant, organization, or application, so risk scoring reflects each environment's actual threat surface from first operation.
Extended Security With External Intelligence
- Pull scores from any platform, third-party threat intelligence, and security tools via API, so every existing investment contributes signal to the LOA calculation.
- Build analyzers for internal telemetry, SIEM data, or application logs without modifying the core engine or disrupting existing analyzer operations.
- Tune the model per organization, so scoring reflects your actual threat surface, not a generic baseline designed for a different environment.

Can Your Security Team See Which Sessions Are High-risk Right Now?
The average breach takes 204 days to detect. Continuous trust evaluation reduces that to under a minute.
Real-time risk visibility
See every active session's trust score in real time. Drill into contributing signals: device, network, behavior, location.
Automated threat response
Define risk thresholds and automated responses. Step-up, terminate, alert, or escalate based on your security policy.
Zero Trust compliance evidence
Continuous verification meets the letter and spirit of Zero Trust mandates. Full audit trail of every risk evaluation.
204 days
Average time to detect a breach (IBM 2025)
< 1 min
Assurance Authority detection time
4x signals
More signal categories than traditional SIEM-based detection
Ready to see how Assurance Authority evaluates Your Risk In Real Time?
Schedule a technical walkthrough, no deck, just your actual use case.
Request a Demo