Authentication Verifies the Credential. We Verify The Operator.
Presence Authority verifies the right person is at the screen throughout the session, not just the credentials used at login, with continuous presence verification.
Human Presence Assurance · Infection Protection · Data Loss Controls
43%
Of breaches involve unattended terminals
< 2s
Departure detection time
100%
Screen capture prevention
Problems We Solve
Close the Security Gap After Login
Once a session is authenticated, most platforms stop watching. Sensitive data stays exposed, unauthorized viewers go undetected, and audit trails go silent, leaving a gap that policies alone cannot close.
Authentication Cannot See the Screen
MFA, conditional access, and session controls verify the credential. What they were never designed to answer is whether the authenticated operator is the same person at the screen. Every unverified minute where sensitive data sits exposed is a gap your existing stack has no visibility into.
Policies Cannot Stop a Phone Camera
Phone cameras and shoulder surfing operate entirely outside every digital security tool in your stack. In remote and hybrid environments, screen capture happens in the physical world where no policy, DLP tool, or endpoint control can reach.
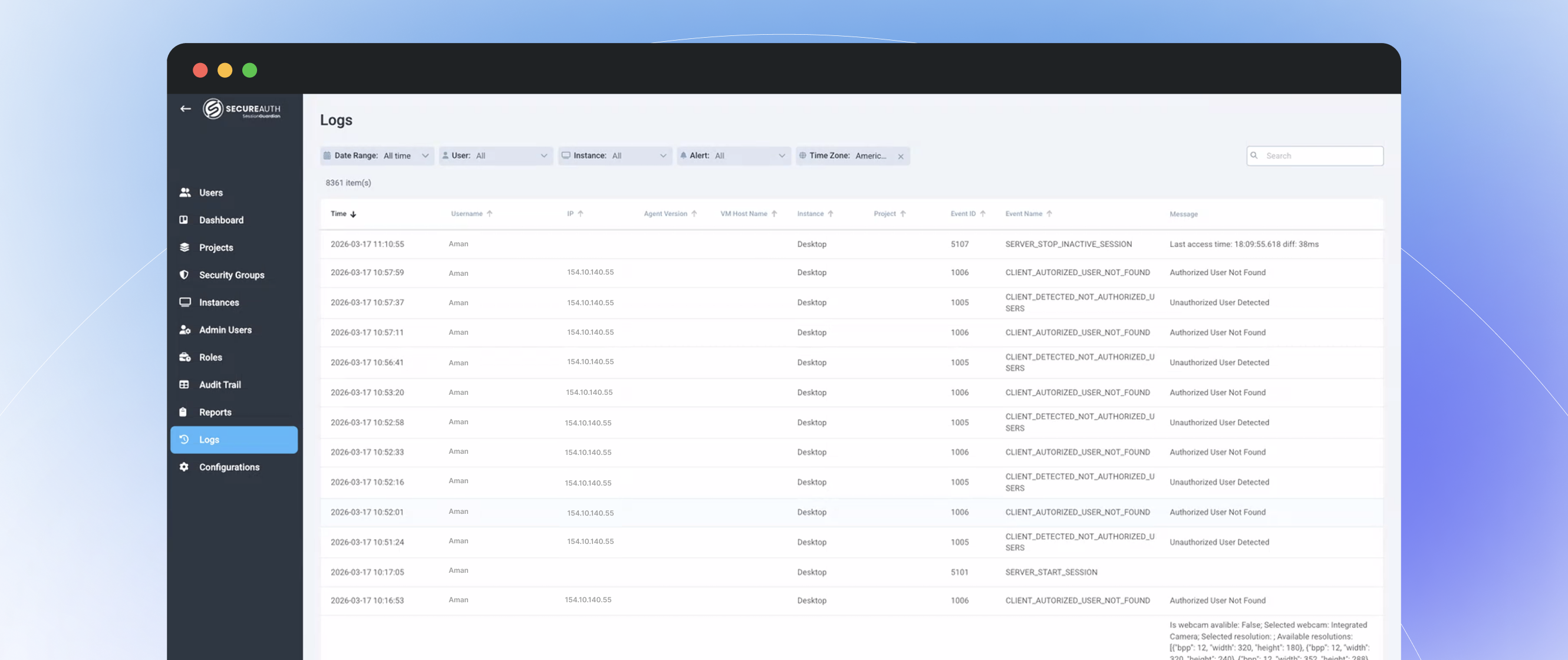
Login Records Don't Satisfy Auditors
Login timestamps don't answer what auditors actually ask. Without session-level proof that the authorized operator was present and active, investigations drag, audit prep bloats, and vendor approvals stall on questions your current logs cannot answer.
CONTINUOUS PROTECTION FROM LOGIN TO LOGOUT
Core Capabilities
Verifies Operator Presence
- Add continuous facial verification alongside your existing authentication controls to confirm the authorized operator remains at the screen, not just at login.
- Auto-locks the session when the operator steps away and resumes it instantly on return, with no passwords or re-authentication prompts required.
- Answer the question your IAM stack was never designed to ask not whether the credential is valid, but whether the right person is using it right now.
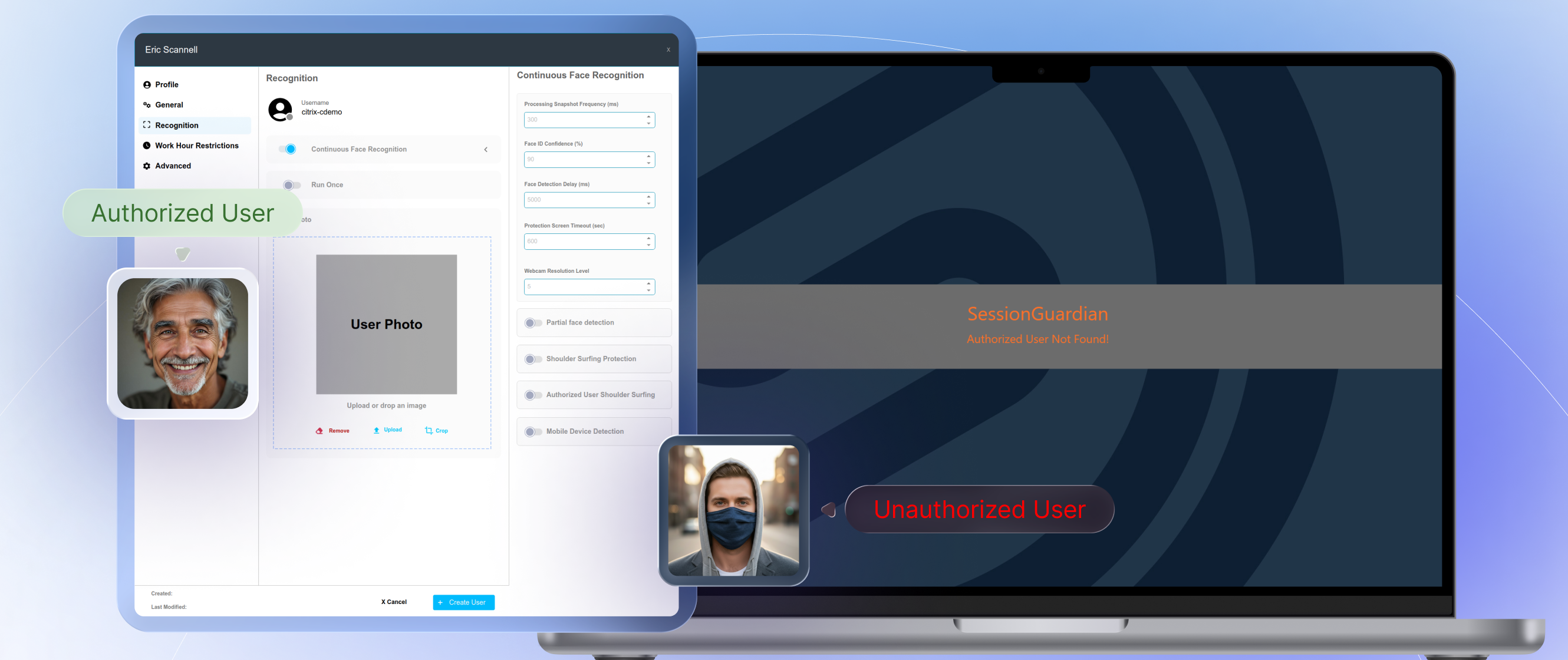
Block Screen Capture
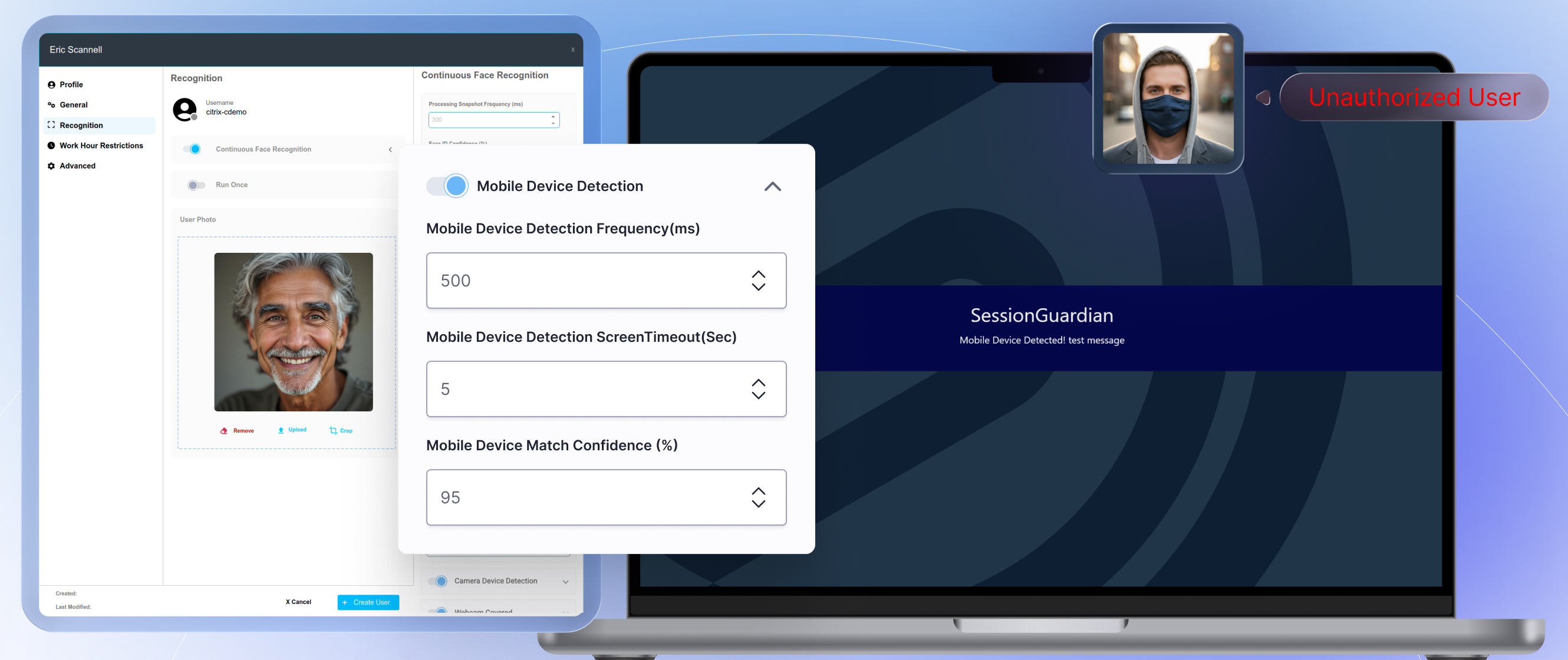
- Detect mobile phones and cameras in the webcam field of view before capture occurs, so sensitive data never reaches an unauthorized device.
- Blocks screen share and screenshots at the session level, so restrictions apply continuously, not just at the point of access.
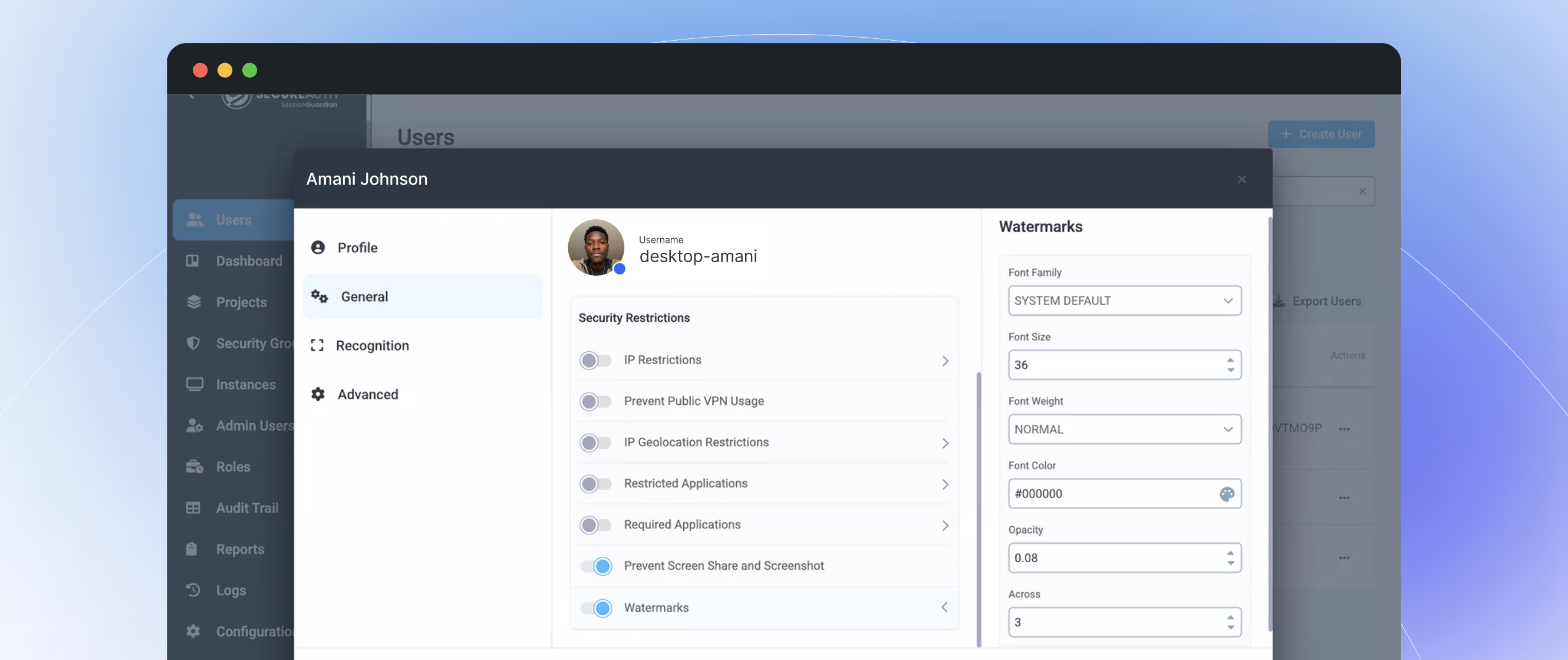
- Apply dynamic watermarks that make every piece of on-screen data traceable, so exposure is contained even when prevention fails.
Controls That Work Throughout The Session
- Sensitive data doesn't leave the workspace through screenshare, screenshots, or file transfers. Controls run at the session level, continuously, without depending on user behavior or manual policy enforcement.
- Apply controls that operate independently of user behavior or policy awareness, so protection does not depend on the operator making the right choice.
- Close the data loss path that endpoint and DLP tools leave open once a session is live and the credential is trusted.
Session Evidence Without Surveillance Infrastructure
- Biometric data never leaves your environment. Facial verification runs locally or on-premises, with nothing stored or transmitted externally. GDPR compliance by architecture, not by policy.
- Generate granular audit trails, event logs, and SIEM-ready outputs so compliance teams get the session-level documentation they need without the surveillance infrastructure they don't want.
- Give investigators continuous presence records that answer the questions login timestamps cannot, so audit prep shrinks and vendor approvals move faster.
Why CISOs Choose Continuous Operator Verification
43% of insider threat incidents involve unattended workstations. Physical presence is the gap your identity stack doesn't cover.
Physical security meets digital identity
Bridge the gap between logical access control and physical presence. Know that the authenticated user is the one viewing the data.
Data loss prevention at the screen level
Screenshots, screen recordings, and shoulder surfing are data exfiltration vectors your DLP stack can't see. Presence Authority covers them.
Zero-trust all the way to the chair
True zero trust doesn't stop at the network edge or the login screen. It extends to the physical presence of the authorized user.
43%
Of insider threats involve unattended terminals (Ponemon 2025)
31%
Of data leaks via screen capture
26%
Of data exposure from shoulder surfing in shared spaces
Ready to see how Presence Authority protects Your Active Sessions?
Schedule a technical walkthrough, no deck, just your actual use case.
Request a Demo